Issue
Call to a .NET Framework assembly on a network folder fails with error:
"Could not load file or assembly 'file://\\server\path\file.dll' or one of its dependencies. Operation is not supported. (Exception from HRESULT: 0x80131515)
Troubleshooting
In this particular case, I wanted to call an assembly with tests which had been deployed using Team Build to a shared folder, then use MSTest in the command line to run them.
MSTest behaved differently depending on whether it is being called from a Windows 2008 R2 Standard server or Windows 8 Client. Using the following command line:
MSTest /testcontainer:\\server\path\file.dll /detail:debugtrace /detail:traceinfo
- From Windows 8 client, user as local administrator: command works as expected. It loads the tests and executes them.
- From Windows 2008 R2 Standard, user as a local administrator: command fails with the following message:
Could not load file or assembly 'file://\\server\path\file.dll' or one of its dependencies. Operation is not supported. (Exception from HRESULT: 0x80131515)
Further troubleshooting using 1) a mapped drive 2) PowerShell 3) /testcontainer parameter between quotes show that all these would also fail under Windows 2008 R2 Standard.
The error “Could not load file or assembly” (0x80131515) is a catch-all error. For instance, it is also reported when the exe or dll was downloaded from an unsafe zone. This is fixed by right-clicking the assembly and choosing “Unlock” from the General tab. Sometimes the “Unlock” option won’t show, and in this case it wasn’t.
Blocking is done based on a Zone Identifier alternate stream that is added to a file when it is copied from the Internet. To validate that the file is actually blocked, display this Zone Identifier using the following command (note the direction of the “<” sign – the opposite one would erase the file):
more < file.dll:Zone.Identifer
If ZoneId = 3 or 4, your file is blocked. In our case, the files show no alternate Zone.Identifier stream.
Since copying the files locally to a folder in the Window 2008 R2 Standard server allowed MSTest to execute the tests, this showed that the issue was constrained to some security policy differences between Windows 8 and Windows 2008 R2 Standard. This also confirmed that the files were not blocked.
Next step I looked into the .NET Framework security policy configuration. Using the instructions from this Microsoft blog post I modified the CAS policy settings using the following command prompt:
CasPol.exe -m -ag 1.2 -url file://\\server\path\file\* FullTrust
This added the following record into the CAS policy (CasPol.exe -l):
1.2. Zone - Intranet: LocalIntranet
1.2.1. All code: Same site Web
1.2.2. All code: Same directory FileIO - 'Read, PathDiscovery'
1.2.3. Url - file://\\server\path\file\*: FullTrust
This did not resolve the issue as expected, but the following error started to be reported on the Event log:
Log Name: Application
Source: VSTTExecution
Description:[…]
(MSTest, PID 2000, Thread 1) AssemblyEnumerator.EnumerateAssembly threw exception: System.IO.FileLoadException: Could not load file or assembly 'file://\\server\path\file.dll' or one of its dependencies. Operation is not supported. (Exception from HRESULT: 0x80131515)
File name: 'file://\\server\path\file.dll' ---> System.NotSupportedException: An attempt was made to load an assembly from a network location which would have caused the assembly to be sandboxed in previous versions of the .NET Framework. This release of the .NET Framework does not enable CAS policy by default, so this load may be dangerous. If this load is not intended to sandbox the assembly, please enable the loadFromRemoteSources switch. See http://go.microsoft.com/fwlink/?LinkId=155569 for more information.
By following the link recommended in the log, I got more information on the issue and how to solve it with the configuration switch loadFromRemoteSources.
From MSDN documentation:
“In the .NET Framework version 3.5 and earlier versions, if you loaded an assembly from a remote location, the assembly would run partially trusted with a grant set that depended on the zone in which it was loaded. For example, if you loaded an assembly from a website, it was loaded into the Internet zone and granted the Internet permission set. In other words, it executed in an Internet sandbox. If you try to run that assembly in the .NET Framework version 4 and later versions, an exception is thrown; you must either explicitly create a sandbox for the assembly (see How to: Run Partially Trusted Code in a Sandbox), or run it in full trust.
The <loadFromRemoteSources> element lets you specify that the assemblies that would have run partially trusted in earlier versions of the .NET Framework are to be run fully trusted in the .NET Framework 4 and later versions. By default, remote assemblies do not run in the .NET Framework 4 and later […]. If you set enabled to true, remote applications are granted full trust.
If <loadFromRemoteSources> enabled is not set to true, an exception is thrown under the following conditions:
- The sandboxing behavior of the current domain is different from its behavior in the .NET Framework 3.5. This requires CAS policy to be disabled, and the current domain not to be sandboxed.
- The assembly being loaded is not from the MyComputer zone.”
And, in the same article:
| In the .NET Framework 4.5, assemblies on local network shares are run as full trust by default; you do not have to enable the<loadFromRemoteSources> element. |
This part of the documentation also shows why it worked on Windows 8: .NET Framework 4.5 is the default for Windows 8.
For validation purposes, I originally applied the recommended setting to machine.config, which is too wide. Later I tested with just MSTest.exe.config and it also worked, which is a smaller recommended scope.
Resolution
[Verified] Add the following entry to the MSTest.exe.config file (at C:\Program Files (x86)\Microsoft Visual Studio 11.0\Common7\IDE):
<configuration>
<runtime>
<loadFromRemoteSources enabled="true"/>
</runtime>
</configuration>
or
[According to documentation] Use .NET Framework 4.5.
Brian Harry highlighted in his latest post how Gartner had included Visual Studio and TFS in the Leaders quadrant for the second year in a row! Here is a picture of it:

I had never heard of Soasta/Tricentis/Test Plant/Original Software, I will have to check these ones out.
This report, along with the other one on ADLM tooling makes for an interesting analysis: Microsoft has an edge over ADLM quadrant leaders in that some of the others (Rally for instance) do not not even show up here. I will come back to that later.
Last month I went to a nice presentation at the Austin TFS User Group on migration from TFVC format to TFS Git, using Git-TFS, a very useful one, the kind that makes you want to research more after it.
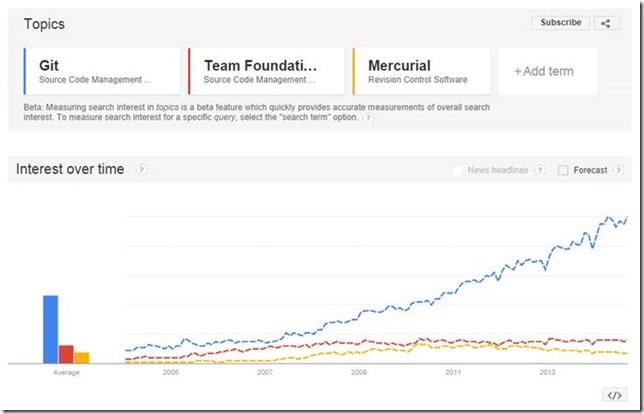
However one of the first slides of the talk did a comparison using Google trends which was used as a justification to moving to Git, because according to it, TFVC was going nowhere, whereas Git was exploding in adoption (notice that the numbers are not absolute, that is they are normalized. For instance, if you have just TFS and Mercurial, the number for TFS will be different).
![clip_image001[6] clip_image001[6]](http://clearmindsoftware.com/image.axd?picture=clip_image001%5B6%5D_thumb.jpg)
I had in the had past previous encounters with skewed statistics, so I waited until the Q&A at the end to ask a few questions about it.
I pointed out that since we were seeing data that had been filtered through Google search, it did not take into account that most Microsoft tools users however would first go to the MSDN site first and search from there (or just press Help from Team Explorer), so some of the millions of people who have MSDN and use TFVC are not being represented.
Also, git has many client providers, such as Xcode to Tortoise-git. Most of them are also OSS with “best-efforts” support, meaning “if you have an issue, search in the Internet for a solution”. So in a way this trend curve also reflects a bit of where the information sources are for git related topics in general, it is a bit fragmented so you need to go through a search engine to have it all collected for research.
The most important data point I observed is that the TFVC curve (numbers aside) were pretty much stable. So “where is git interest growth coming from?” since the TFVC interest curve seemed pretty stable.
I recalled that around 2001 I had seen something similar about Linux adoption in the desktop: some pointed how it was growing so fast that it would overtake Windows soon. This growth curve was similar, steady but slightly rising for Windows, and steeper for Linux, showing it overtaking Windows in the forecast.
Time showed that the market shares were not changing that much, so where was the Linux growth coming from? Sun took too late to realize that it was their own Unix, Solaris (and for that matter, all of Unix variants) that were being cannibalized as people moved to Linux. Later Sun made Solaris into open source but it was already too late: most Unix users had converted to Linux.
If we could use “searches” as a proxy to “interest”, and that as a proxy for market share: with git growing and TFVC stable, what was the “Solaris” equivalent that was being replaced?
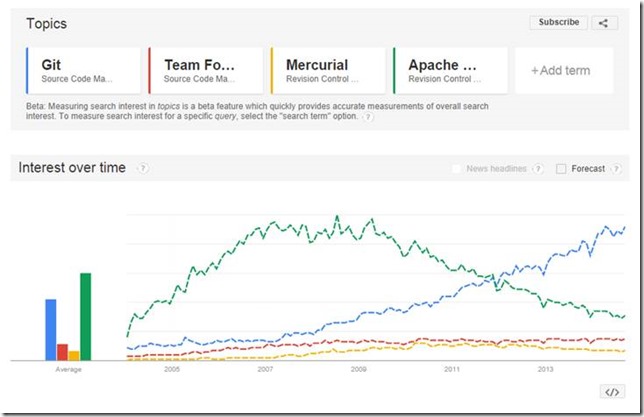
After I explained my point of view, the presenter went online and added Mercurial in the graph… there is surely a downwards trend on Mercurial queries, but that does not explain how git searches were growing:
I mentioned Subversion to him but we didn’t have time to try it out so I continued from home.
I then added Subversion, listed under “Apache Subversion Revision Control System” to the graph, and voilá, the puzzle was solved: the new trend graph, confirmed that the open source community (and for that matter, Microsoft TFS users as well) is readjusting its preferences. Git is now as popular as Subversion was in the 2007-2009 time frame. The growth of interest in git is pretty much explained by the winding down of searches on Subversion and Mercurial, and probably some from TFVC now migrated to TFS git:
I then continued my research looking for the development of Interest in other source control systems, starting by the all-time grandfather of many, CVS. Back-extrapolating its curve, you can see that it was very popular, but was itself run over by Subversion in the 2005 time frame:
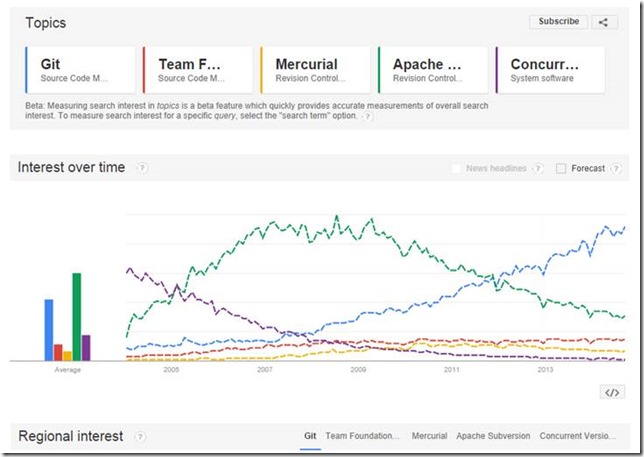
I then tried out with others: Rational ClearCase, Rational Jazz Source Control, Perforce. Out of these, only Perforce showed a small but steady curve. ClearCase is now reduced to just a trickle, and Jazz Source Control did not even show up. Finally I had to see if any record of Visual Source Safe still existed after 2005, and as expected it dwindled after 2005:
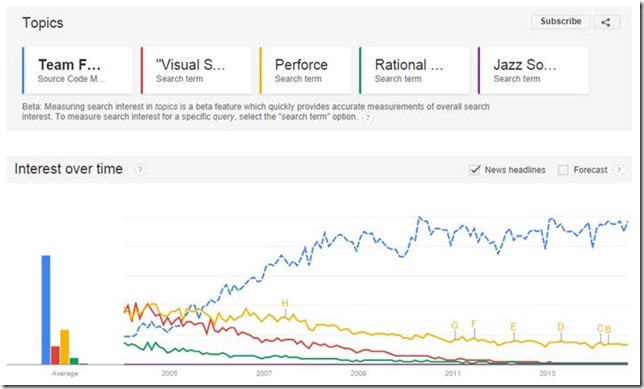
As a final experiment I tried the “Forecast” feature which seems to trace a simple extrapolation based on the data so far (forecast starts at ABC points below). The extrapolation confirmed the steadiness of the TFVC curve so far, and the ongoing dwindling of Subversion as it gets overtaken by git as all other open source version control systems:
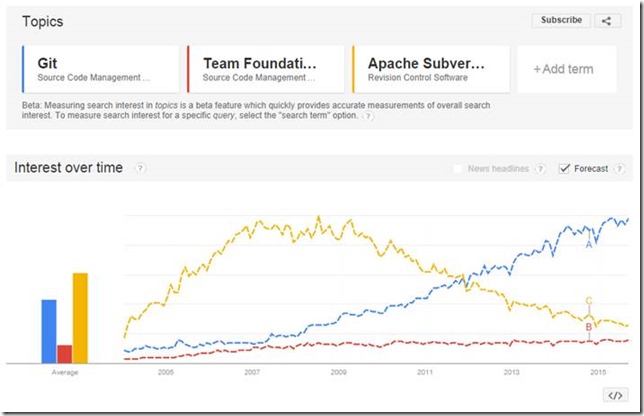
So in conclusion:
- Git will become to open source version control systems what Linux is to open source Unix-like systems;
- TFVC will remain stable for the foreseeable future, with users of TFS-git adding to the number of git adopters;
and
- You can use statistics to justify any point of view, so be on the lookout for any inadvertently skewed perspectives;
- Do not just accept the data, think about it too – logic will help you in finding the hidden aspects (the “Solaris”) of the question;
If you have read so far and have a different perspective, please let me know what your thoughts are on this.